So, you came back? You like me, you really like me! No? You just like Lync… I get it…
Let's continue where we left off… Part 1 of this Lync 2010 Edge Server series.
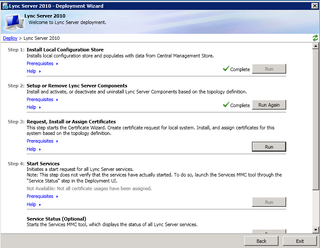
We ended last time after getting the Edge added to the topology. The topology was exported and copied to the Edge server. We prepped the Edge server, installed the Lync bits, imported the topology, and installed the Lync components based on that topology.
We are now here:
And it's now time to deal with certificates. But, before you click "Run" on Step 3, we need to do a little more preparation on the Edge. Part of our next process will be requesting certificates from our Internal CA. Since the Edge is **NOT** domain joined, we need to import the internal CA certification chain into the Edge "Trusted Root Certificates" store.
Start by making sure you have access to the Internal CA – if your edge isn't in a DMZ, like my example, this is easy. You may need a hostfile entry to resolve the name of the CA. If you ARE in a DMZ, you may need a hostfile entry, and you may need to open firewall ports. As I mentioned last time, this post, is a nice aggregation of information.
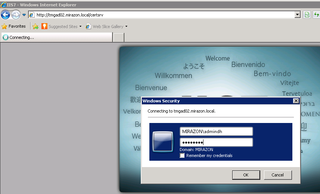
To test to see if you have access, open a browser on your edge and go to https://fqdn.ca.local/certsrv
Great – we can. Now authenticate & click OK.
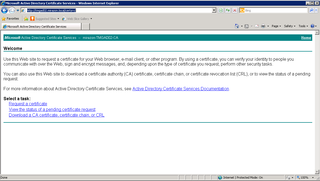
We want to download our CA certificate.
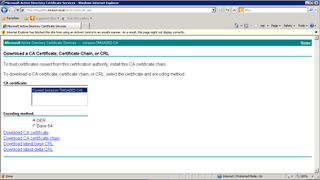
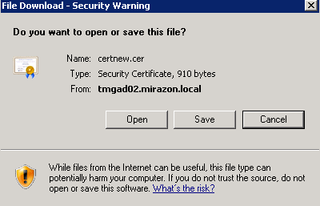
Yup. Get the DER CA Certificate.
Save that somewhere useful – like C:source
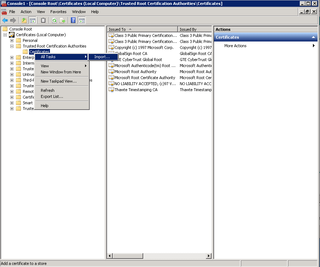
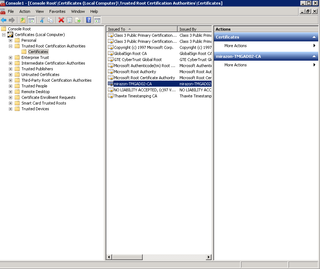
Now, open up your MMC and get the Certificates – Local Computer – Snapin loaded. We are going to import that certificate.
We want to IMPORT that into the Trusted Root Certificate Authorities
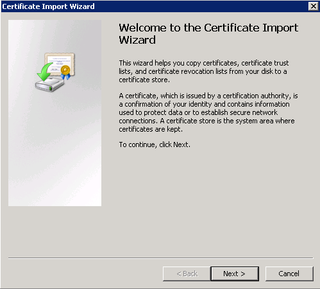
Yes, Click Next.
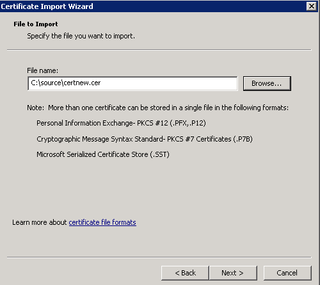
Go get that certificate we just downloaded from the Internal CA. Click Next.
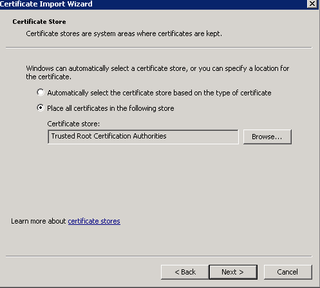
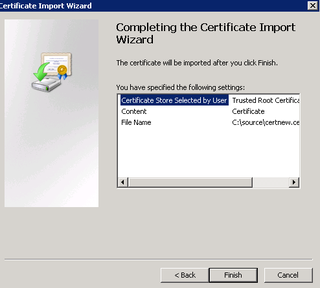
Yes, this is where we want it. Click Next.
Verify. Finish.
Yay. Ok.
Great. Now, go back to the Deployment Wizard.
NOW We're ready to click Run on Step 3.
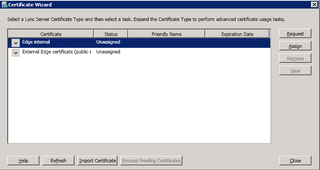
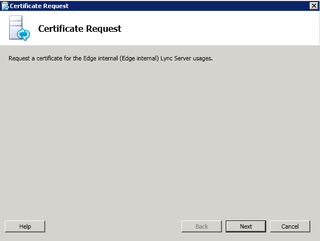
We're wanting to Reqest the Edge Internal Certificate.
Next.
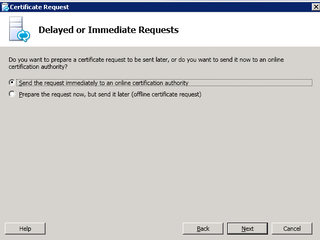
We are going to do this immediately. Click Next.
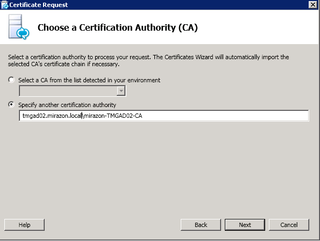
Enter your CA information – This is CaSe SEnsiTIVe here. Click Next.
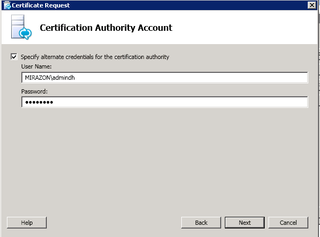
We need to authenticate – remember, we are not Domain Joined. Click Next.
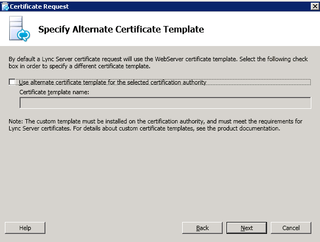
Next.
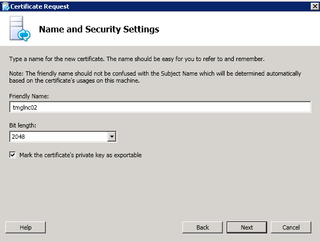
Give your certificate a friendly name, 2048, and exportable key. Click Next.
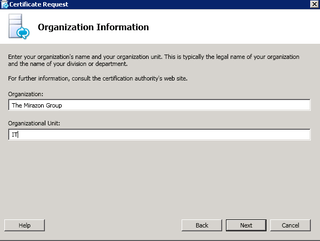
Cert info, Click Next.
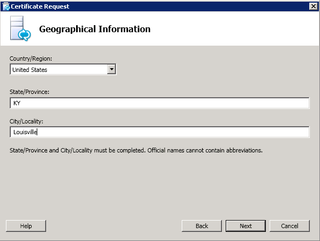
Cert Info. Click Next.
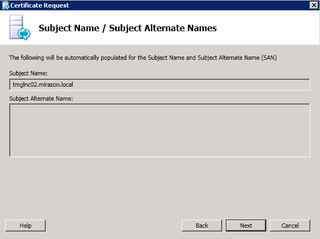
This is our certificate SN. Click Next.
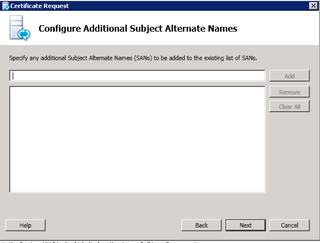
Add SANs if needed. We don't. Click Next.
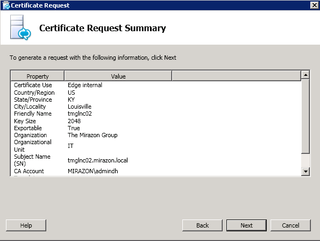
Verify. Click Next.
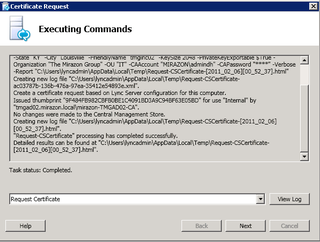
Success! Click Next.
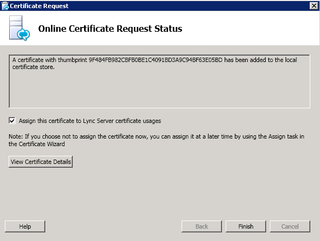
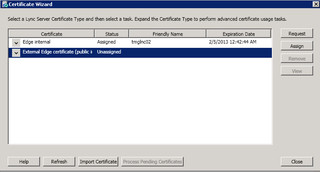
We've requested a certificate, our Internal CA responded and sent it back. Lync knows this, and is now ready to make it wok. Check the "Assign" box and click Finish.
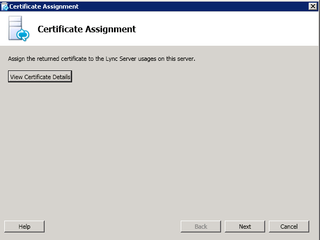
Next.
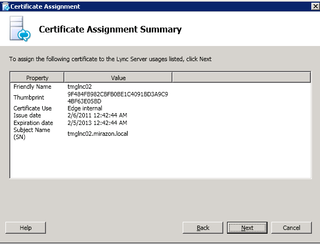
Summary. Next.
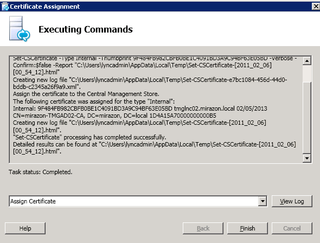
Completed. Finish.
Great. We're done. We've got the Lync Edge Internal Certificate requested, received, imported, and assigned to Lync.
Let's stop here for today. More next time – we'll actually do the Public/External certificate.

So I’m stuck at the part where I need to ‘Run’ step three (Request, Install, or Assign Certificates) But it won’t let me click on the ‘Run’ button (option is grey’d out). It says: “Not available: Local machine not present in local configuration store”
Any ideas??